January 2013
Intermediate to advanced
384 pages
9h 54m
English
This design pattern is a cornerstone of fault-tolerant programming and is also useful for resource-allocation issues. It tells you how to keep track of events and to take action only when the frequency of the events is larger than you're willing to allow.
Figure 23-2 shows the general principles of Leaky Bucket Counter. Error reports fill the bucket, while an allowable number of errors is deducted from the bucket constantly as it leaks. If the rate at which the bucket fills is larger than the leaking rate, an error is triggered.
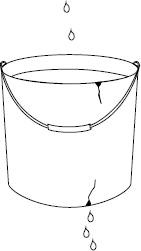
Figure 23-2: Principles of Leaky Bucket Counter.
Leaky Bucket Counter is from my book Patterns for Fault Tolerant Software (Wiley).
Read now
Unlock full access