Incentives 85
ing bogus prior transaction records). To tackle this problem, Feldman et al.
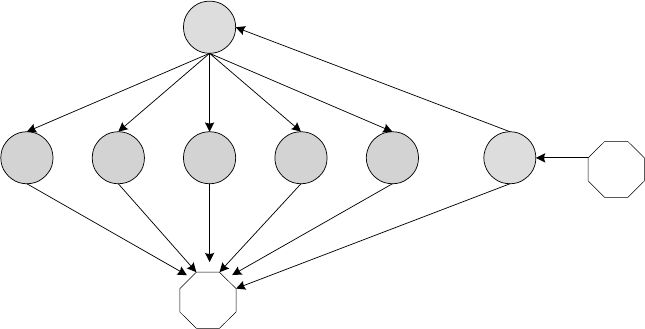
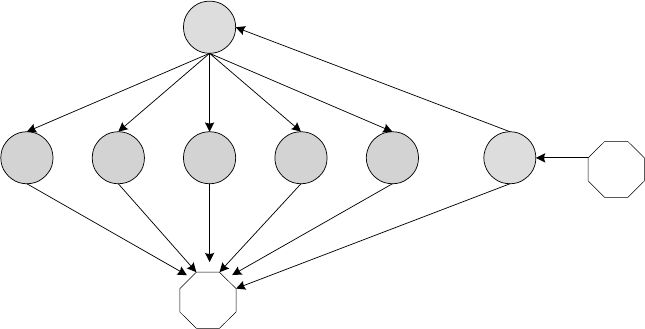
suggested a graph theoretic technique. To illustrate, consider the reputation
graph shown in Figure 5.2. Here, each no de in the graph represents a peer (C
denotes a colluder) and each directed edge represents the perceived reputation
value (i.e., the reputation value of the node incident by the edge as p erceived
by the node originating the edge). We can see that the colluders give each
other a high reputation value. On the other hand, a contributing peer (e.g.,
the top node) gives a reputation va lue of 0 to each colluder because the con-
tributing peer does ...