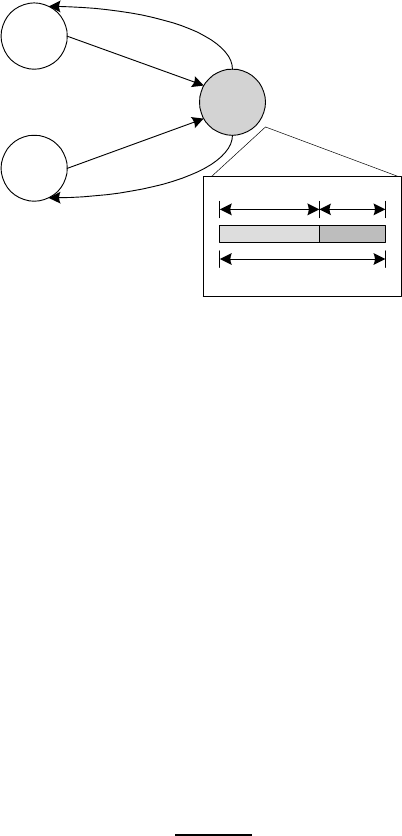
90 Peer-to-Peer Computing
N
1
N
2
N
S
Submitting bids
1
b
2
b
1
t()
x
2
x
S
W
1
x
2
x
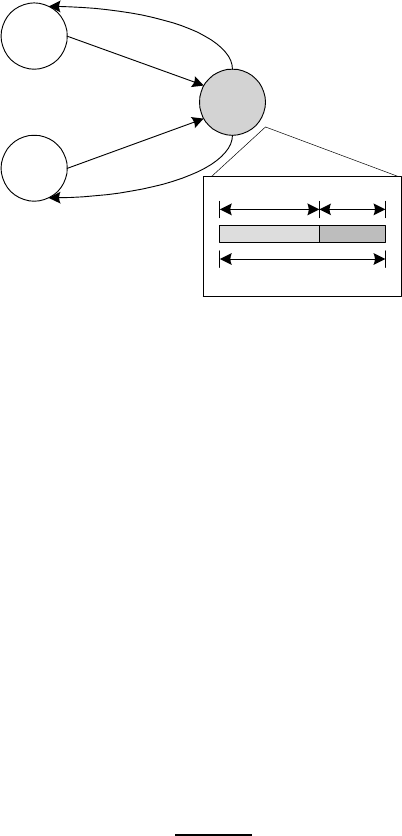
Bandwidth Allocation
Result
t()
t()
t()
t()
t()
FIGURE 5.5: Two file requesting peers (N
1
and N
2
) compete for uploading
bandwidth of a source peer (N
S
) [Ma et al., 2004a].
where:
N
X
i=1
x
i
≤ W
S
(5.9)
Here, the loga rithmic function represents the utility as perce ived by each
peer i.
The above optimization problem can be solved by a progr e ssive filling
algorithm that prioritizes competing peers in descending order of the marginal
utility C
i
/(b
i
+ x
i
).
Given values of b
i
and C
i
, the source peer can compute the allocations in
a deterministic manner. However, from the perspective of a requesting peer,
a pro ...