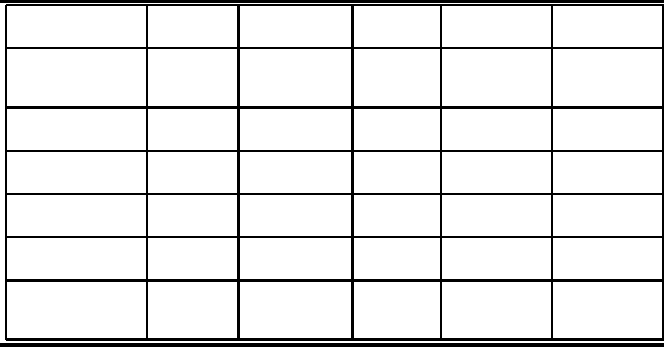
154 Peer-to-Peer Computing
TABLE 6.2: Comparison of popula r symmetric trust esta blishment schemes
in WSNs.
Scheme Energy
awareness
Memory
consumption
Network
resilience
Network
connectivity
Additional
requirement
Eschenauer [Es-
chenauer and
Gligor, 2002]
Average High Poor Average None
Jolly [Jolly et al.,
2003]
Very good Very low Poor N/A None
Chan [Chan et al.,
2005b]
Good High Good Average Attack proba-
bilities
Du [Du et al.,
2004]
Good Low Average Good Location
information
Liu [Liu et al.,
2005a]
Average High Good Average None
Eltoweissy [El-
toweissy et al.,
2006]
Average Low Good Average None
plementation of asymmetric cry pto graphic protocols in resource-constrained ...