September 2017
Intermediate to advanced
314 pages
8h 5m
English
Once you have identified suspicious activity on a machine, you can collect an investigation package to identify the current state and further understand the tools and techniques used by the attacker. This information is useful to gather prior to isolation and rebuilding of the computer as part of your recovery process; otherwise, the information is lost and you may never discover how the attack occurred.
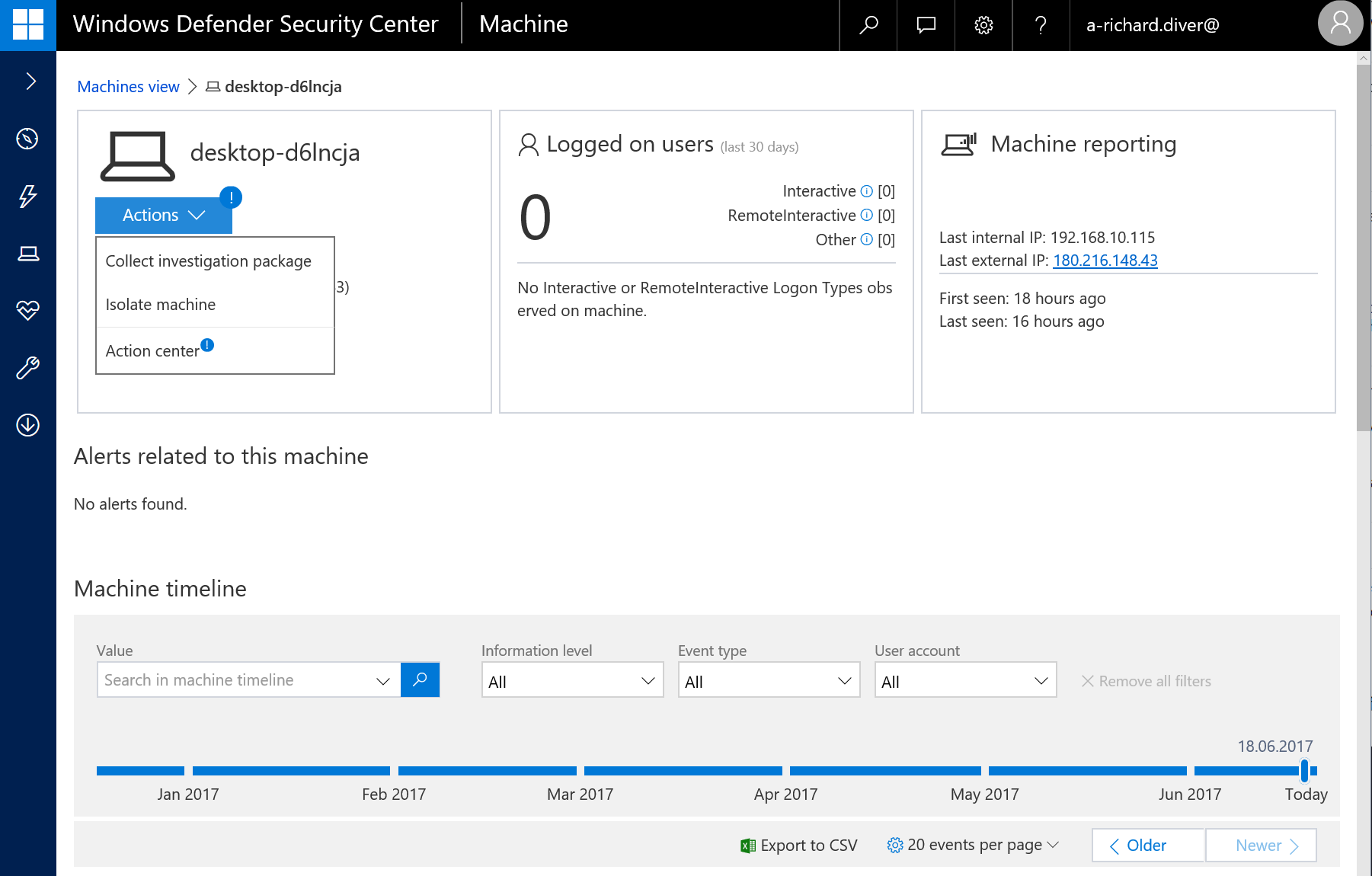
To initiate a collection, find the machine in the ATP portal, go to the Actions menu, select Collect investigation package, and then enter a reason when prompted:
It is recommended you run this report on ...
Read now
Unlock full access