To test how an actual exploitation works, you can use a vulnerable application made by Snyk (https://github.com/snyk/goof). To run this application, you need to have Node.js and MongoDB installed and properly running in your target server.
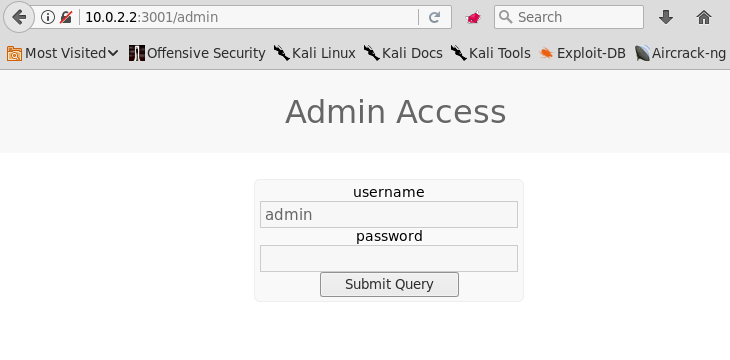
You should try an injection attack that bypasses the password check in the admin section. Having a proxy set up, browse to the admin section of your vulnerable application. In this example, it will be http://10.0.2.2:3001/admin. If you submit the user admin and any password, you can see that no access is given.
If you send that request to Repeater, you can see that it is sending ...

