June 2019
Intermediate to advanced
308 pages
7h 21m
English
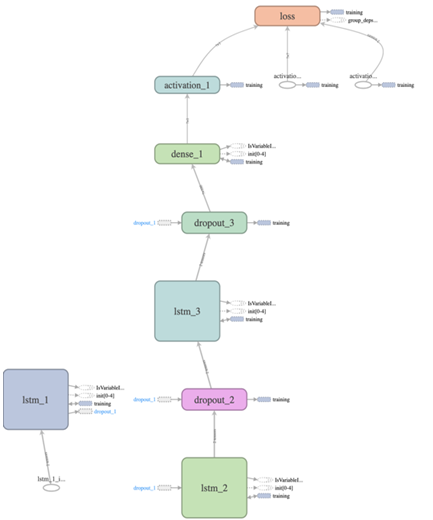
We considered a three-LSTMs-layered network architecture for the CPU utilization based host/device-level intrusion detection. The following diagram presents the LSTM architecture we used:
We can train and test the model by running the lstm_anomaly_detection.py file (available in the chapter's code folder) as follows:
python lstm_anomaly_detection.py
Read now
Unlock full access