Time for action – Wireless Eavesdropping
Follow these instructions to get started:
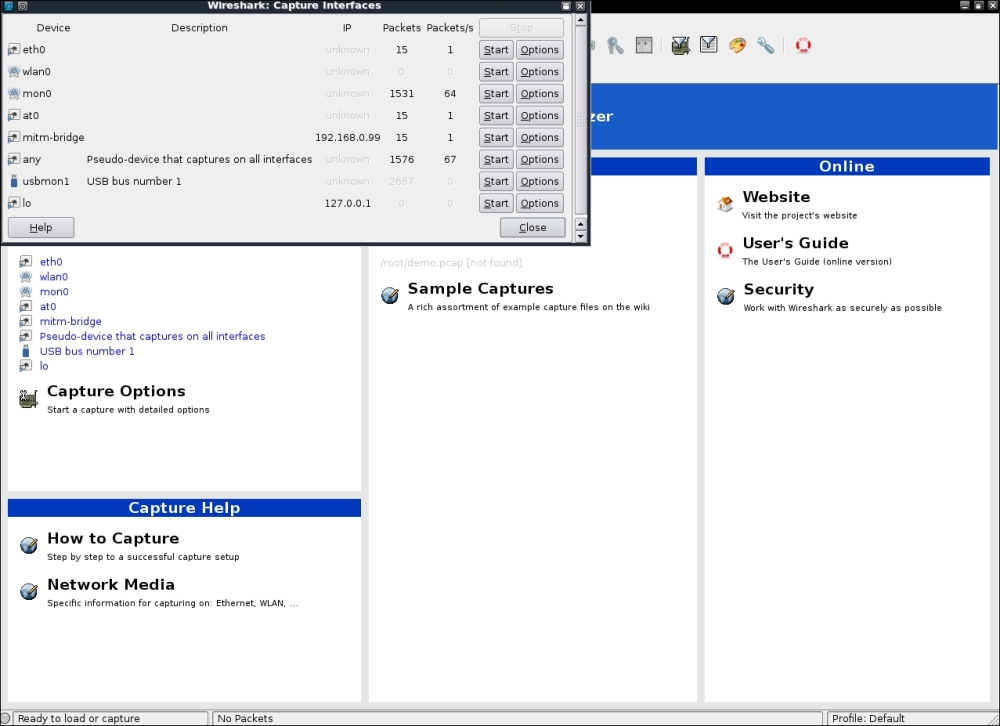
- Replicate the entire setup as in the previous lab. Fire up Wireshark. Interestingly, even the MITM-bridge shows up. This interface would allow us to peer into the bridge traffic, if we wanted to:
- Start sniffing on the
at0interface so that we can monitor all traffic sent and received by the wireless client: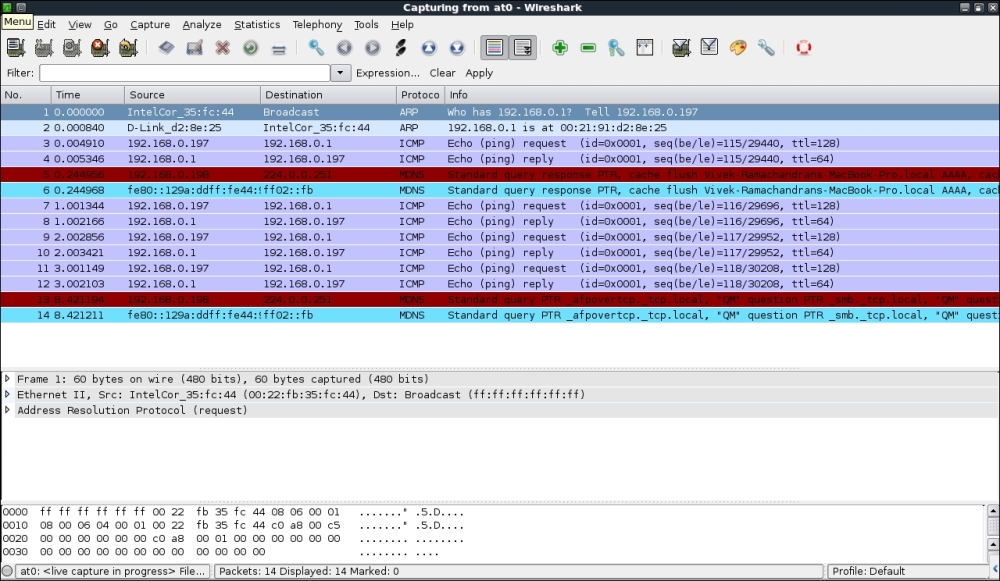
- On the wireless client, open up any web page. In my case, the wireless access point is also connected to LAN and I will open it up by using the address
http://192.168.0.1 ...
Get Kali Linux Wireless Penetration Testing : Beginner's Guide now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

