June 2018
Beginner
510 pages
13h 7m
English
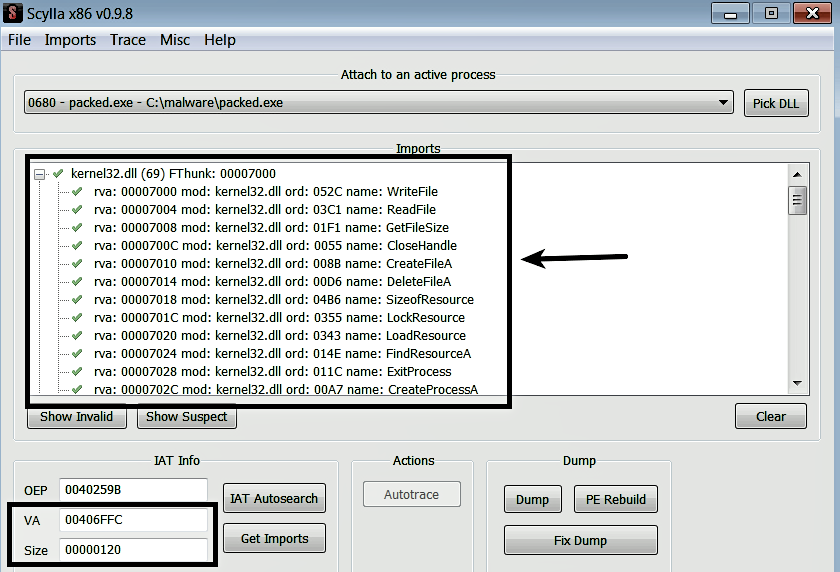
To fix the imports, go back to Scylla, and click on the IAT Autosearch button, which will scan the memory of the process to locate the import table; if found, it populates the VA and the size fields with appropriate values. To get the list of imports, click on the Get Imports button. The list of imported functions determined using this method is shown here. Sometimes, you may note invalid entries (with no tick mark next to the entry) in the results; in such case, right-click those entries and choose Cut Thunk to delete them:
After determining the imported functions using the previous step, you need to apply the ...