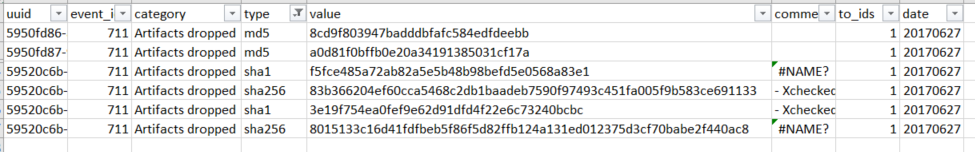
A good deal of tools that can ingest threat intelligence are available to incident response analysts. For example, disk forensic platforms discussed in Chapter 8, Analyzing System Memory, have the ability to ingest hashes from threat intelligence feeds to search for IOCs. In addition to commercial disk forensic tools, the Autopsy platform can conduct searches against a hash set. Navigating back to the export format in MISP, there is the ability to download a .csv file of the event indicators. For event 711, download the CSV file. Next, filter the data and select on hash values in the type column. This produces the following list: