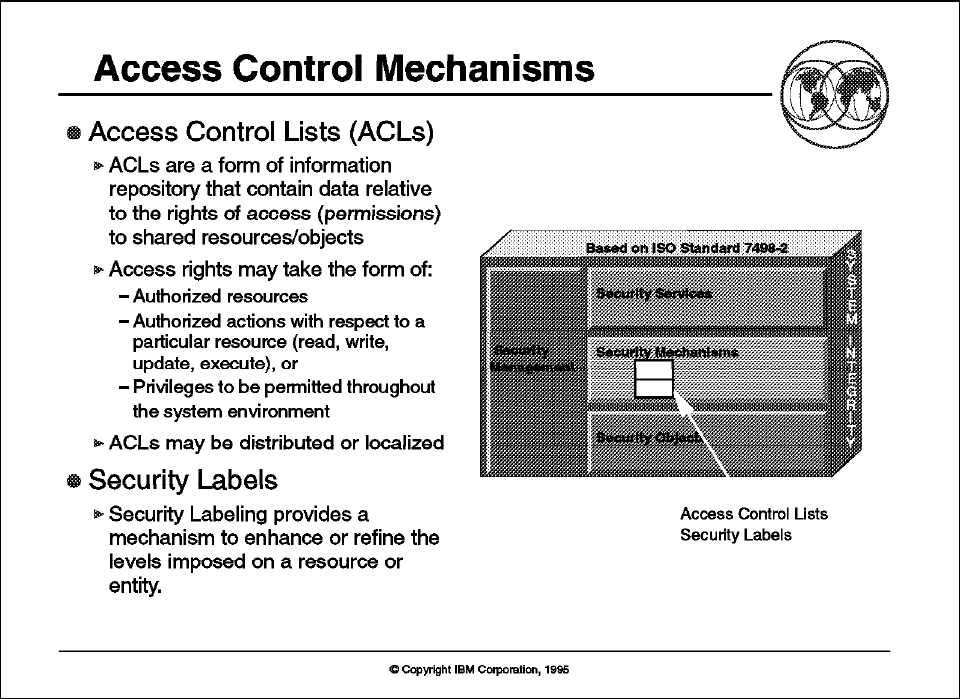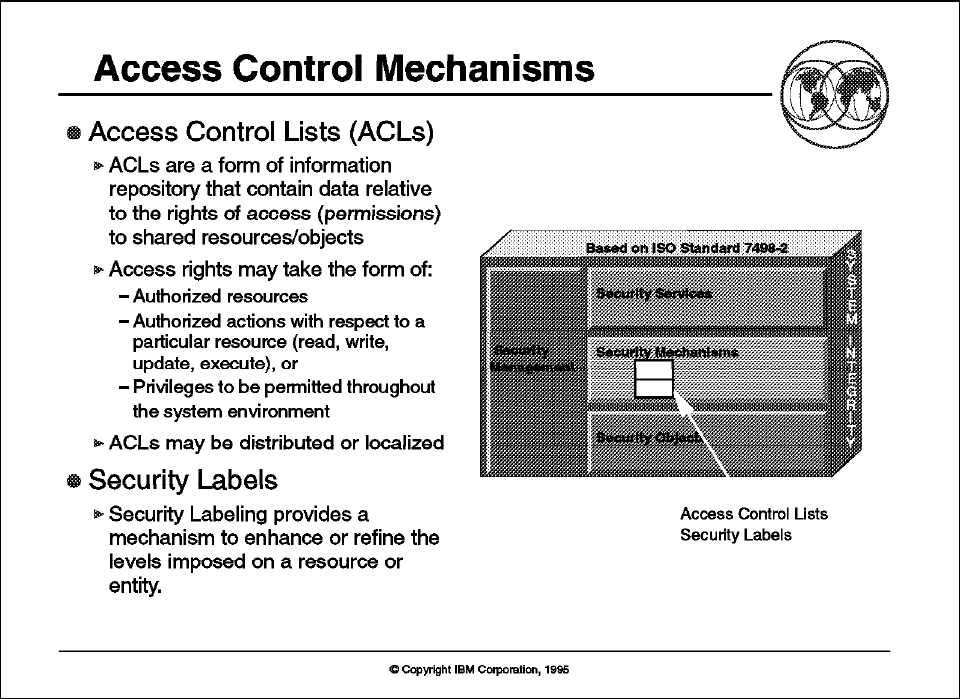
2.3.8 Access Control Mechanisms
Figure 23. Access Control Mechanisms
Key Points
Access control services are implemented by access control lists and/or security
labels.
Presentation Script
Access Control Lists:
Access control lists (ACLs) are a form of information
repository that contain data relative to the rights of access (permissions) to
shared resources/objects granted to authenticated users of the system. The
access rights might take the form of authorized resources, authorized actions
with respect to a particular resource (read, write, update, execute), or privileges
to be permitted throughout the system environment. Access control lists are
categorized ...