64 Chapter 3: MPLS Security Analysis
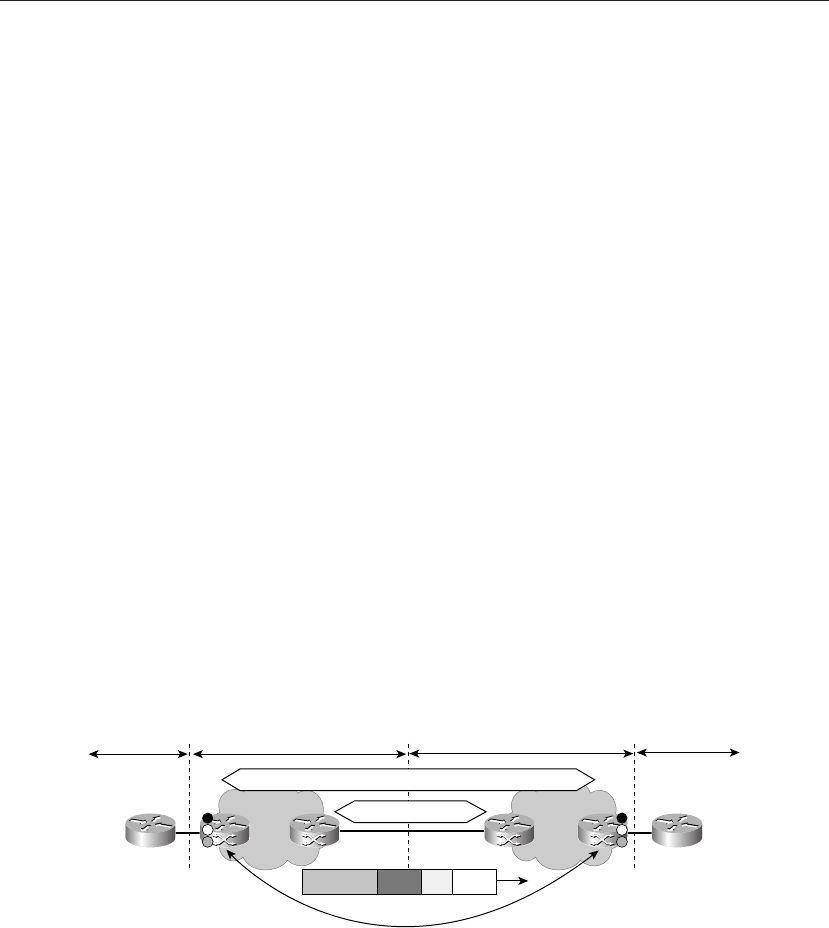
In comparison with model A, model B is more scalable in that it requires only one
connection between the ASBRs over which all VPNs are propagated. For this to work,
MP-eBGP must be run between the ASBRs, and traffic is exchanged with labels. This can
be secured adequately, but with more configuration the likelihood of error and a subsequent
security breach increases.
Model B still requires each ASBR to hold the VPN routes for each shared VPN, and this is
another scalability concern. To solve this issue, model C was invented.
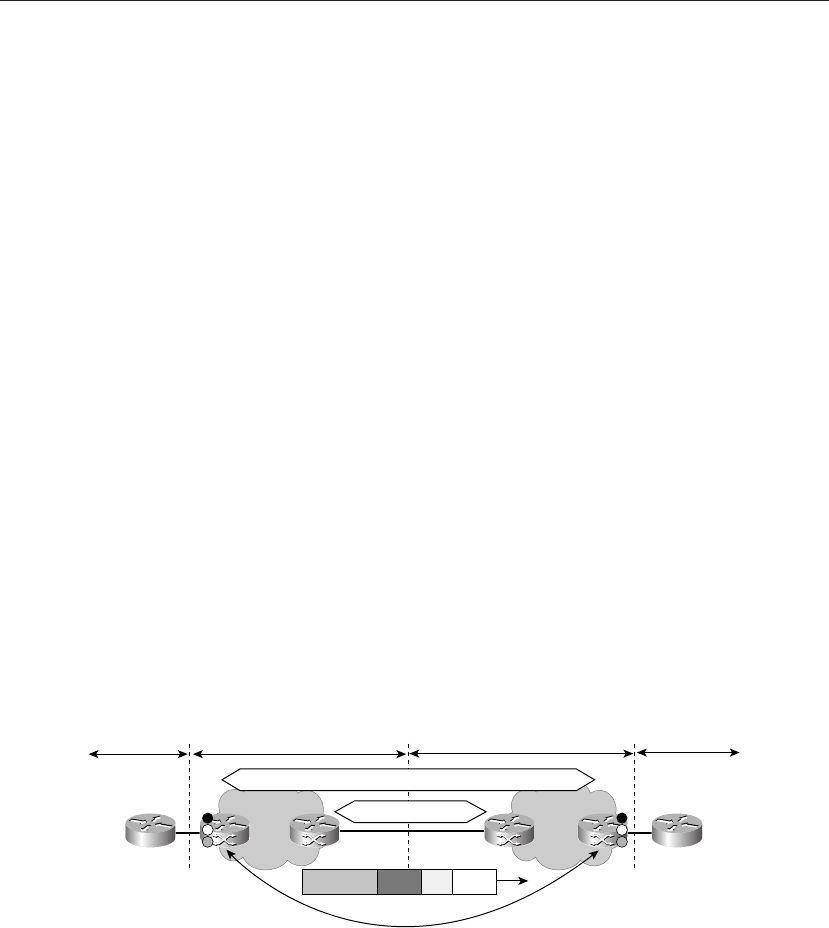
Model C: Multihop eBGP Redistribution of Labeled VPN-IPv4 Routes
Between Source and Destination ...