Location of the IPsec Termination Points 205
The alternative would be to run IPsec between CEs, but this situation would be more
complex because typically the number of CEs is significantly higher than the number
of PEs.
Except in special cases, PE-PE IPsec currently is not much used for security reasons. It
is clearly not a generic solution for VPN security. CE-CE IPsec should be used in those
cases.
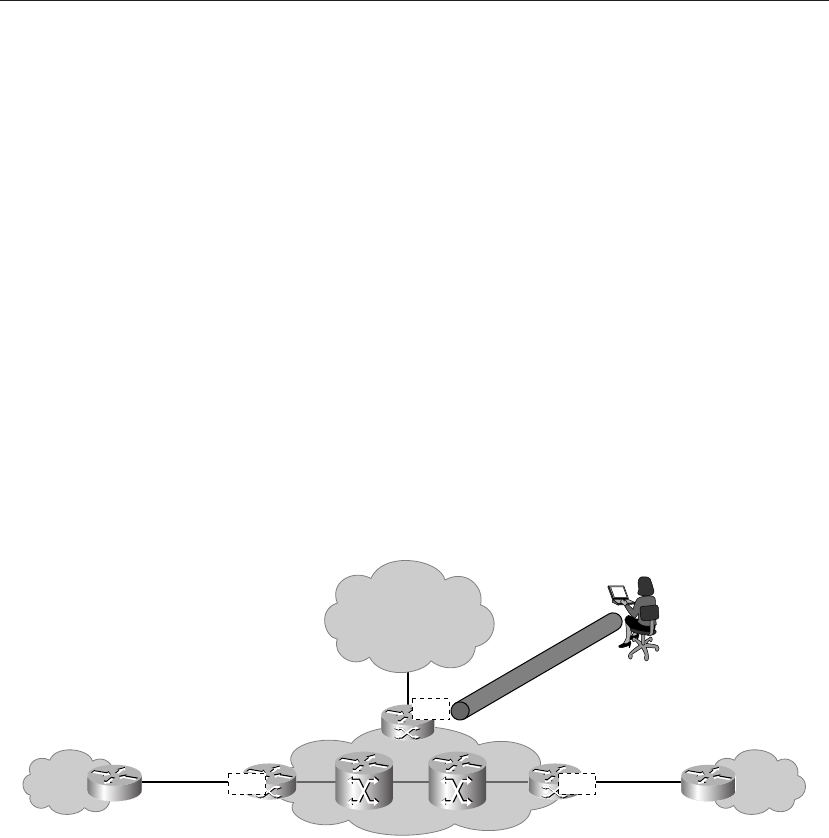
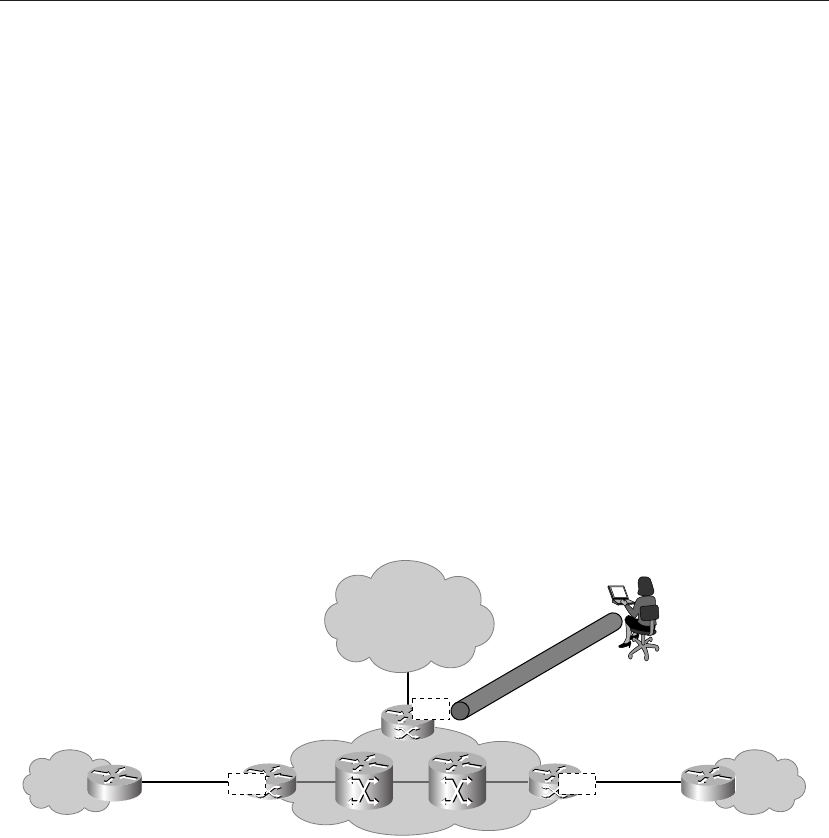
Apart from using IPsec between CE-CE and PE-PE, there is a third form of using IPsec: as
a way of remotely accessing a VPN.
Remote Access IPsec into an MPLS VPN
In enterprise networks, teleworkers connect to their home networks via VPN: this used ...