76 Chapter 3: MPLS Security Analysis
Other MPLS services, such as the Pseudo Wire Emulation (PWE), also implement point-to-
point services based on Layer 2, where direct CE-CE visibility is possible.
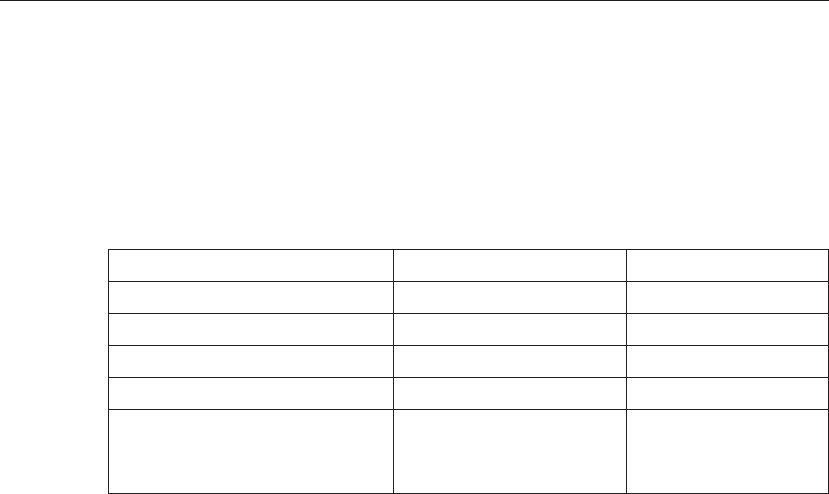
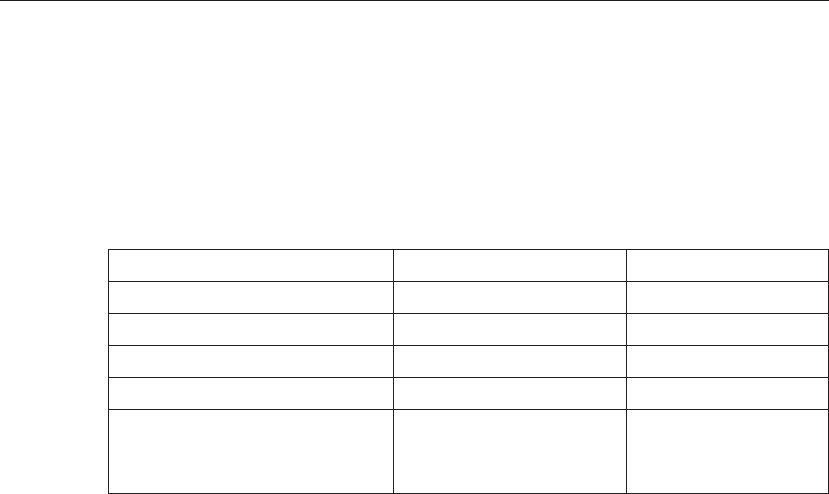
Comparison of VPN Security Technologies
Table 3-2 compares all the aspects of VPN security for the different VPN technologies.
Overall, at the time of writing this book, the industry had mostly accepted that both MPLS
and ATM/Frame Relay can be operated securely. It was also common understanding that
operational issues such as misconfigurations are an issue for any VPN technology.
Summary
In this chapter, we defined common requirements that VPN users hav ...