200 Chapter 6: How IPsec Complements MPLS
Location of the IPsec Termination Points
In an MPLS VPN environment, IPsec can be applied at various points of the network:
• Within the VPN sites—For example, end-to-end IPsec security. (This case will not
be discussed further here because here security is completely independent of MPLS.)
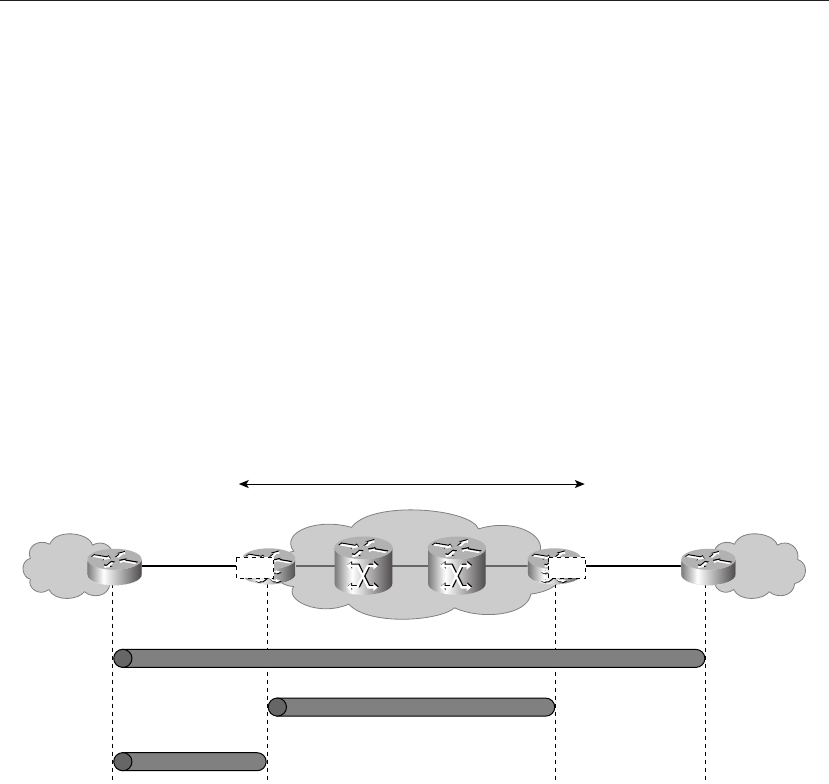
• Between CE routers of the VPN—In this case, the MPLS core is also not involved
in the security services. The trust of this solution depends on whether the party who
manages the CE is trusted or not.
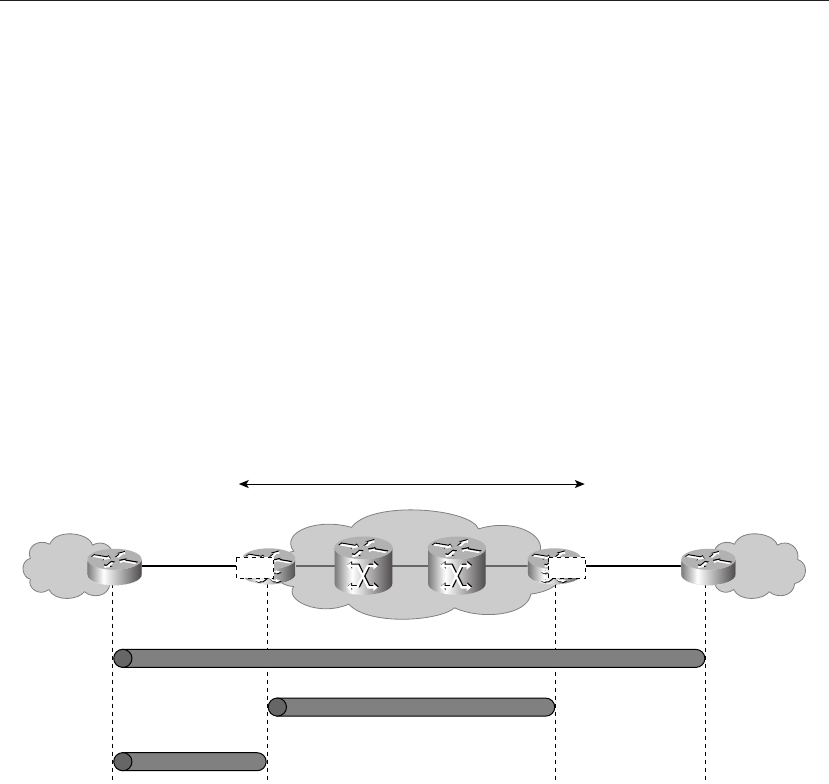
• Between PE routers within the MPLS VPN core—Here, the service provider is
managing the IPsec services and the VPN customer ...