Summary 193
— Use MD5 for LDP in the core.
— Use MPLS over L2TPv3 when considering an MPLS over IP deployment
scenario for best practice security.
See Appendix A for a detailed configuration example of a provider edge router.
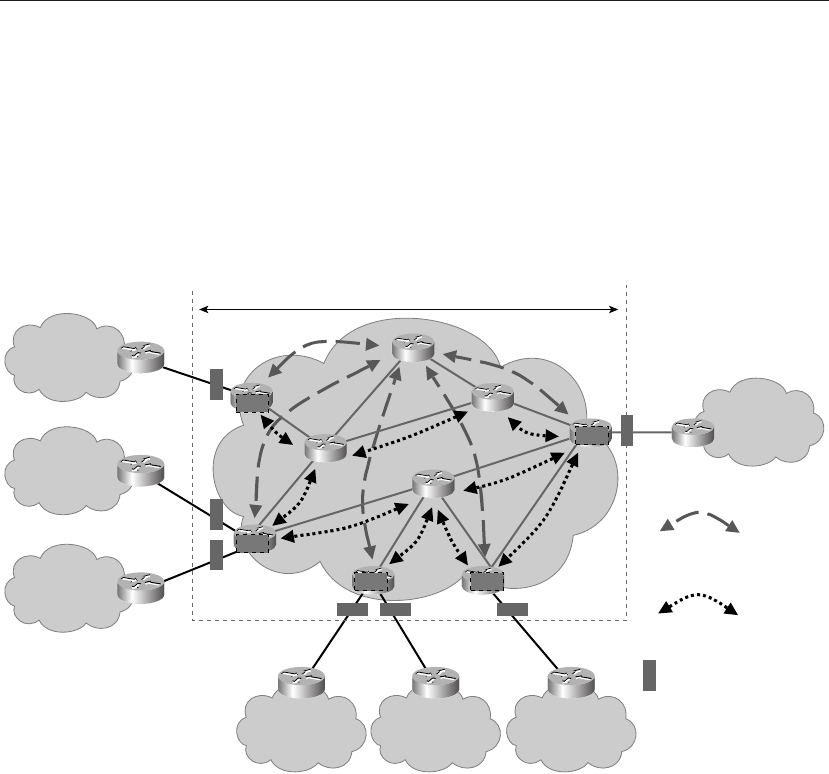
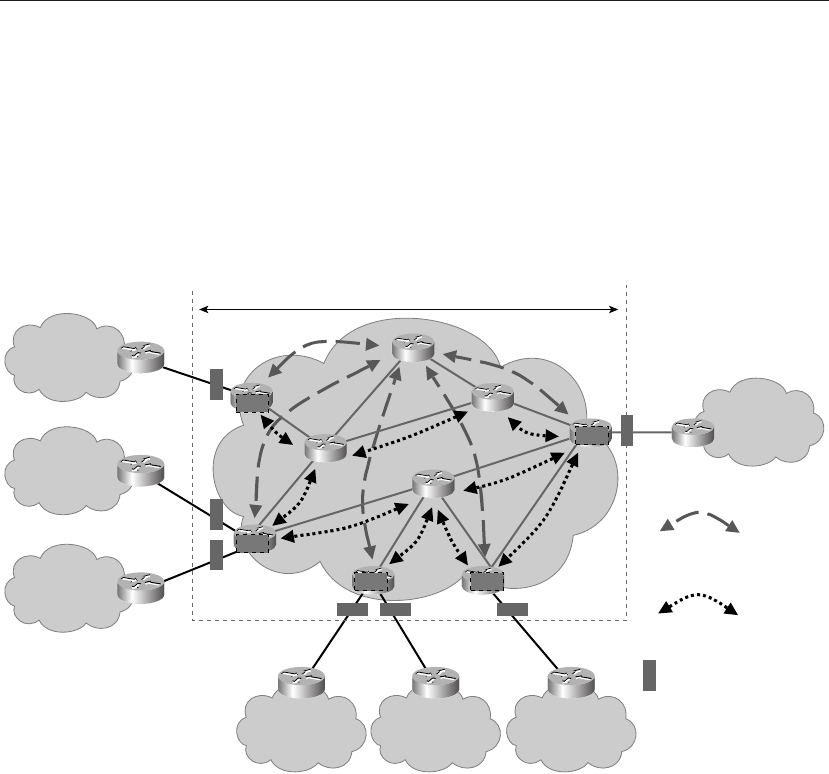
Figure 5-2 depicts the requisite best practice functions for each of the network components,
such as P, PE, and CE.
Figure 5-2 Securing the MPLS Core
Summary
In this chapter, we provided an operational overview of security considerations for
each MPLS VPN component—for example, P, PE and CE. Using a building block approach
in order to understand essential service and topological factors that affect security
mechanisms, we hav