March 2008
Intermediate to advanced
911 pages
20h 31m
English
Finally, the cool part. This is where we get to specify, declaratively, that a given resource/method combination is accessible only by users in certain roles. Most of the security work you’ll do is probably with <security-constraint> elements in your DD. (Lots of picky rules later.)
<security-constraint> element in the DD:

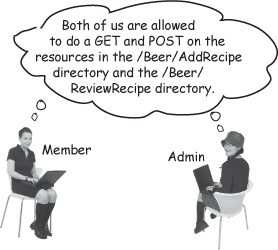
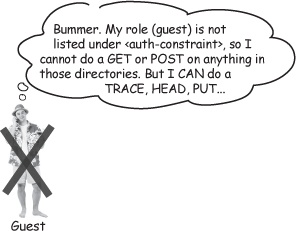
Because they’re in the “Member” role, Diane and Annie can do GET and POST on resources that fit the <url-pattern> elements. Ted is only a “Guest”, so he can’t do a GET or POST.