Implementing Security from Scratch
As I mentioned in the introduction, it is entirely possible and quite easy to build a robust security model using nothing more than a simple database table and a small bit of CFML code. Consider the portal example we created at the end of Chapter 7. This application is the perfect candidate for implementing security from scratch.
If you refer back to Chapter 7 for a moment, to Figure 7-6,
you’ll remember that we said security for the portal could be
handled by three templates: Application.cfm,
Login.cfm, and
Validate.cfm. Both authentication and
authorization functions are handled by these templates. If you look
at Figure 8-1, you’ll see the basic flow of
the authentication/authorization process. Note that this view differs
slightly from the one in Chapter 7 due to the
addition of two new templates that handle user registration.
Don’t worry about them for the time being, we’ll get to
them soon enough.
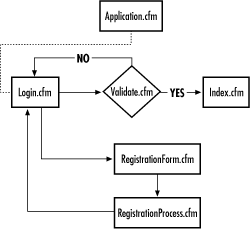
Figure 8-1. Security scheme for the portal application
Creating a Simple Security Table in the Database
The first step to building
security into the portal application is to create a database to store
username and password information. Table 8-1 shows
the schema for a single table called Users that
will store our profile and security information.
Table 8-1. Setup for the User Security Table
|
Field Name |
Field Type |
Max Length |
|---|---|---|
|
Username (primary key) ... |
Get Programming ColdFusion now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

