Authentication
Authentication means showing some proof of your identity. When you show a photo ID, like a passport or a driver’s license, you are showing some proof that you are who you claim to be. When you type a PIN number into an automatic teller machine, or type a secret password into a computer’s dialog box, you also are proving that you are who you claim to be.
Now, none of these schemes are foolproof. Passwords can be guessed or overheard, and ID cards can be stolen or forged. But each piece of supporting evidence helps to build a reasonable trust that you are who you say you are.
HTTP’s Challenge/Response Authentication Framework
HTTP provides a native challenge/response framework to make it easy to authenticate users. HTTP’s authentication model is sketched in Figure 12-1.
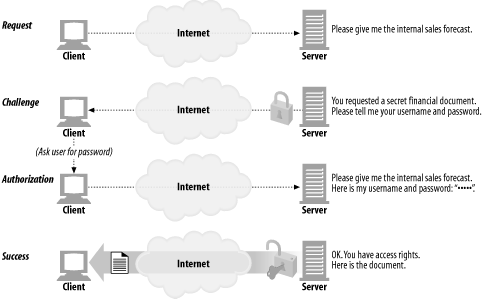
Figure 12-1. Simplified challenge/response authentication
Whenever a web application receives an HTTP request message, instead of acting on the request, the server can respond with an “authentication challenge,” challenging the user to demonstrate who she is by providing some secret information.
The user needs to attach the secret credentials (username and password) when she repeats the request. If the credentials don’t match, the server can challenge the client again or generate an error. If the credentials do match, the request completes normally.
Authentication Protocols and Headers
HTTP provides an extensible ...
Get HTTP: The Definitive Guide now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

