The End-User Experience
When OAuth is being used within an application, the experience for the end user who’s interacting with the application is far less intrusive and complicated than the process that the developer has to go through to implement it.
Implementations of the permission screen, where users accept that the application will perform actions on their behalf, can vary widely depending on the platform on which it is implemented, but the basic principle is the same. The platform displays a page containing basic information about the application and providing a means by which users can permit or deny that application to use their personal data.
Let’s explore what this screen looks like on some of the platforms that currently use OAuth. Twitter’s implementation is as simple as it gets: it presents information about the application requesting access to the user’s profile and provides a simple allow or deny option, as shown in Figure 9-5.
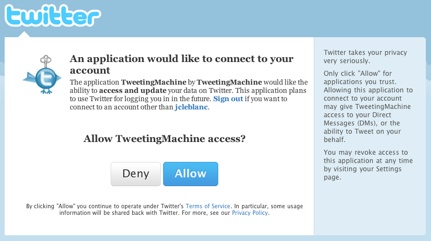
Figure 9-5. The Twitter OAuth authorization screen
Now let’s take a look at an OAuth implementation that is more descriptive. The Yahoo! OAuth process first has the user log in to his Yahoo! account to verify his identity—before even presenting a permission screen to prompt him to accept or decline the application information requirements. This can be a good practice if, for example, a user has set his Yahoo! session to expire every two weeks and ...
Get Programming Social Applications now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

