Step 5: Exchange the Preapproved Request Token for an Access Token
Assuming that the OpenID provider’s response was an approved state containing the preapproved request token, we can now go through the process of exchanging that request token for an access token. This will allow us to make requests to the provider for privileged user resources.
The exchange between the relaying party and provider in this step looks something like Figure 12-3.
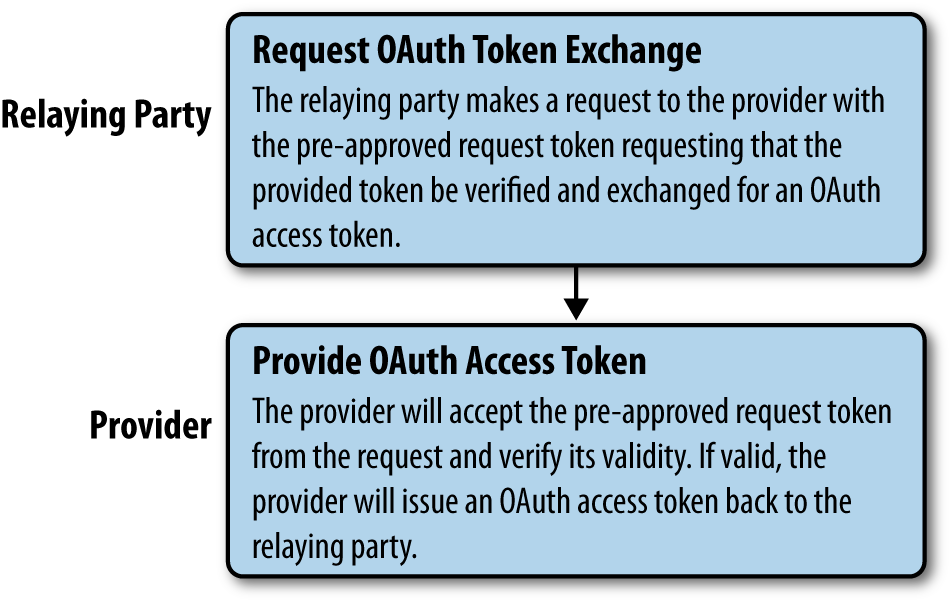
Figure 12-3. Hybrid auth, step 5: Relaying party exchanges the preapproved request token for an access token from the provider
The relaying party will issue a request to the provider to exchange the preapproved request token for an access token. With the exception of the differences in creating a request token object, this step is identical to the request token/access token exchange in the standard OAuth flow.
The provider will check to ensure that the request and token are valid and then return an access token string to the relaying party. The relaying party can then turn that string into an access token object and use it to make signed requests for the user’s privileged data.
Get Programming Social Applications now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

